HACKING TYPES AND TIPS TO STAY PROTECTED
Cell phones - Hackers Next Target!It was bound to happen - they have hacked just about everything else. Now it's the cell phones. Cellphone hacking has just recently surfaced and been made public ever since some one did some cellular phone hacking on Paris Hilton's cell phone. This article will give you some information about what is going on out there and what you can do to better protect your cell phone information.

What Does It Involve
The fact of someone hacking cell phone became public knowledge when Paris Hilton's cell phone, along with her information was recently hacked. Unfortunately for her, all her celebrity friends and their phone numbers were also placed on the Internet - resulting in a barrage of calls to each of them.
Cell phone hackers have apparently found a glitch in the way the chips are manufactured. The good news, though, is that it only applies to the first generation models of cell phones that use the Global System for Mobile communications (GSM). Another requirement is that the hacker must have physical access to the cell phone for at least three minutes - which is a real good reason not to let it out of your sight. Currently, although the problem has been remedied (at least for now) in the second and third generation phones, it seems that about 70% of existing cell phones fall within the first generation category.
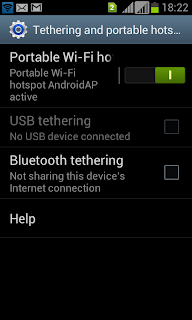
Another way that mobile phone hacking can take place is for a hacker to walk around an area with people that have cell phones and a laptop that has cellphone hacker programs on it. Through an antenna, and a little patience, his computer can literally pick up your cell phone data - if it is turned on. This is more applicable to cell phones that use Bluetooth technology.
The fact of someone hacking cell phone became public knowledge when Paris Hilton's cell phone, along with her information was recently hacked. Unfortunately for her, all her celebrity friends and their phone numbers were also placed on the Internet - resulting in a barrage of calls to each of them.
Cell phone hackers have apparently found a glitch in the way the chips are manufactured. The good news, though, is that it only applies to the first generation models of cell phones that use the Global System for Mobile communications (GSM). Another requirement is that the hacker must have physical access to the cell phone for at least three minutes - which is a real good reason not to let it out of your sight. Currently, although the problem has been remedied (at least for now) in the second and third generation phones, it seems that about 70% of existing cell phones fall within the first generation category.
Another way that mobile phone hacking can take place is for a hacker to walk around an area with people that have cell phones and a laptop that has cellphone hacker programs on it. Through an antenna, and a little patience, his computer can literally pick up your cell phone data - if it is turned on. This is more applicable to cell phones that use Bluetooth technology.
- Steal Your Number
Your phone number can be accessed and obtained by cellphone hacking. This allows them to make calls and have it charged to your account. - Take Your Information
Mobile hacking allows a hacker to contact your cell phone, without your knowledge, and to download your addresses and other information you might have on your phone. Many hackers are not content to only get your information. Some will even change all your phone numbers! Be sure to keep a backup of your information somewhere. This particular technique is called Bluesnarfing.



nice hai
ReplyDelete